Introduction:
Application Programming Interfaces (APIs) are pivotal drivers of digital transformation and rapid modernization within organizations. They are used for communication between critical applications, often interacting with highly sensitive data such as Personal Identifiable Information (PII), making them a prime target for attackers. The growing attack surface from sprawling APIs is complex and often overlooked. APIs can be used for internal use, business to business (B2B), and business to customer (B2C) applications, making tracking and securing them a difficult task. Due to the nature of APIs and how they are developed, maintaining accurate inventories and documentation can be a daunting task. As such, many organizations struggle to understand their API landscape and the accompanying threat landscape.
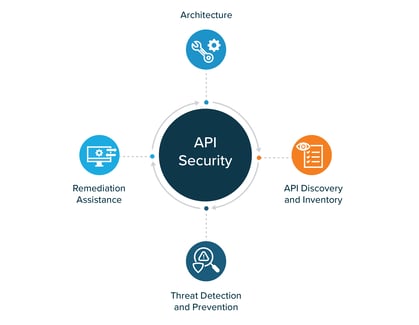
There are four key capabilities API Security solutions should address: the architecture that makes it all function, API discovery and inventory, threat detection and protection, and remediation assistance through vulnerability management and security testing.
Architecture:
The architecture of an API Security product may vary from vendor to vendor. Typically, products have two general approaches to capturing API traffic: inline and out of band. Most vendors have a preferred architecture that works best with their capability set.
Inline solutions provide excellent visibility and real-time threat detection and prevention but should be carefully considered due to architectural constraints. Most inline solutions are built so if the protection services go down, the protected APIs could go down as well. There are steps organizations can take to protect the flow of API traffic during service outages (for example, ensuring the product fails open), but there is a possibility for security to suffer during such outages.
Out of band solutions are simpler to implement because they sit outside of the API traffic, eliminating the need for in-depth architectural considerations. Out of band solutions work by capturing or mirroring the traffic sent to one of several locations. These locations include but are not limited to: API gateways, microservices, load balancers, servers, CDNs, WAFs, and cloud providers. Most out of band solutions work by mirroring traffic, so no agents are required to make the solution work.
API Discovery and Inventory:
APIs can be created in a matter of minutes. The agile nature of API development and the proliferation of microservices can result in uncontrolled API development and API sprawl across an organization. A key component of any API security program is first understanding what is already out there, both internal and external. API security platforms aim to solve this problem by discovering APIs in the environment, including hard to find APIs such as shadow, zombie, or in-development APIs. Discovery and inventory capabilities allow organizations to understand and secure these APIs, as well as assigning ownership of APIs for road mapping and vulnerability management purposes.
Inventory modules of API security platforms can also automate the process of documenting APIs using the OpenAPI/Swagger specifications. This documentation outlines the functionality, data, and responses for a given API. This information may be useful for development teams so they can capitalize on efficiencies by using pre-existing functionality they might not have known about otherwise.
Threat Detection and Prevention:
Threat detection and prevention is a key area for API security products. Unlike API gateways, API security solutions utilize behavioral analysis to find and thwart attacks. API attacks can be immensely complex in nature, so using artificial intelligence to identify attack patterns can be crucial. These attacks may otherwise appear innocuous to the average analyst. Runtime protection is crucial to identify and stop attacks in motion before critical data is exfiltrated or tampered with. Platforms can alert on suspicious activity including an unusual number of requests, the nature of the requests, where the request originated, and more. Additionally, platforms often utilize baselining and anomaly detection to find threats. This functionality allows organizations to discover attacks that may slowly escalate over time or look around for unprotected sensitive data. Comparing all traffic against known baseline activity allows for API security products to quickly identify and stop these attacks before they get access to sensitive data.
Remediation Assistance:
Another key piece of API security is remediation assistance and shift-left development practices. Remediation guidance is crucial for teams to quickly identify threats and patch vulnerabilities in their APIs in a timely manner, before attackers can exfiltrate key data. Some platforms even go further and enable teams to build automated responses and remediation if recurring threats are commonplace in their environment.
While some threat prevention is done after APIs are already deployed, a key part of API security is ensuring the API is developed securely in the first place. This practice is known as shift-left security. Shifting security left can be done in a few different ways. Combining testing methods allows an organization to identify and remediate more vulnerabilities present in their APIs. The two main testing methods are SAST and DAST:
- Static Application Security Testing (SAST)
- SAST is a testing technique that looks for vulnerabilities without running the source code in question. SAST testing primarily looks for coding best practices, programming errors, and vulnerabilities present.
- Dynamic Application Security Testing (DAST)
- DAST differs from SAST, because it is used on deployed APIs. These APIs can be in a development environment or even in production. The main goal of DAST is to identify security vulnerabilities or functionality issues by testing the behavior of APIs in a real-world scenario. Once issues are identified, testers can trace the issues back to the code for remediation.
How K logix Helps
For any API Security challenges, K logix has consulting and advisory services to address your needs. If you are interested in investing in an API Security solution, We work with your team to identify your key requirements, then leverage our vendor agnostic Technology Advisory methodology to determine the best fit solution. If you're interested in learning more, reach out to one of our experts: info@klogixsecurity.com.