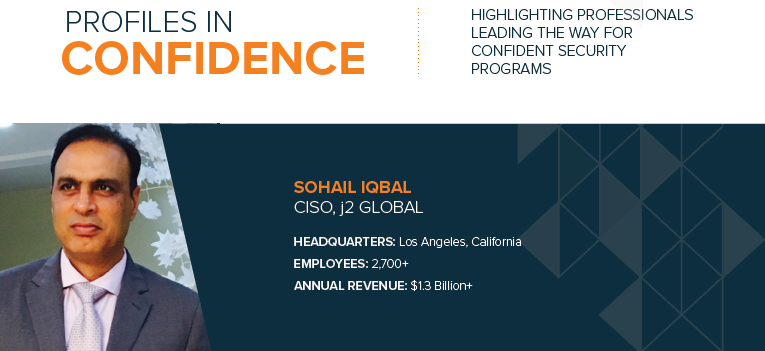
Profile: Sohail Iqbal, CISO, j2 Global
Published On: September 23, 2019
READ SOHAIL'S PROFILE
READ FEATS OF STRENGTH MAGAZINE
When Sohail Iqbal began his career, he worked in pure technologist roles and as his career evolved, he shifted to focus on strategic information security positions. When working at Quest Diagnostics he asked management if he could work on any upcoming audits, something they openly welcomed. He was able to conduct audits and was exposed to learning how to identify security gaps, which sparked his interest in shifting his role to be more focused on information security. He attained his CISSP and moved onto Dow Jones/WSJ where he worked on many projects including their transition to a cloud-first practice. At Dow Jones he was responsible for the strategy to help mature the security posture of many products under the Wall Street Journal including MarketWatch and Barron’s. After eight years at Dow Jones serving as Head of Global Cybersecurity Operations, Iqbal was offered the CISO role at j2 Global.
For over one year, Iqbal has held the CISO role at j2 Global, a leading internet information and services company consisting of a portfolio of 48 brands, reaching over 180 million people per month. j2 Global’s brands include businesses such as PCMag.com, Offers.com, Mashable, and Everyday Health. As the organization continues to acquire a multitude of brands in different verticals, Iqbal is tasked with analyzing the risk and evaluating the security stance at each brand before they join the j2 Global environment.
KEEPING PACE WITH ACQUIRING BRANDS
j2 Global purchases companies at an incredibly rapid pace and they are all integrated into j2 Global’s security program, overseen by Iqbal. He manages security for all j2 Global’s brands, and if the acquired brand had a security person already in place, they would then report into Iqbal.
Iqbal wrote a quantitative analysis for assessing the risk state and identifying gaps for the many brands j2 acquires. He comments, “This quantitative analysis of risk has built significant clarity in terms of portfolios that we bought, how risky they are, how to address gaps, how to prioritize budget, what resources are needed, and the timeline for all of these efforts. It provides a way of estimating what we need to do with each particular organization before they are inducted into our network and we open up our firewalls.”
The biggest challenge for Iqbal is getting to know each of the businesses they acquire since it is not a singular business model, but instead a large portfolio of brands. He must understand each business and their culture, ranging from tech-savvy startups to legacy companies. He explains, “I have to understand the various threat landscapes for each of the brands we acquire, and in some cases understand the legacy nature of operations or cutting edge demands for those portfolios. I have to do an assessment to get a pulse of the business and assess across the organization to see how I am going to customize and cater to each brands’ needs. Every business unit is independent and had their own technology shop prior to being acquired, so I sit down with technology and development leaders to understand their needs and customize the overarching security strategy to address these requirements.”
Iqbal works hard to educate each of the acquired brands that security is not there to block or create hurdles, it is instead there to create a paved road for them to drive their businesses faster. He uses the analogy of security building the right guardrails to make it difficult for cars to veer off the road. He says, “I lead their businesses on the journey that helps them sell more effectively whether it’s making products more secure or achieving levels of compliance.”
QUANTITATIVE REPORTING AND ANALYTICS
Iqbal leverages quantitative reporting and analytics to demonstrate progress and build clarity around the security program, rather than using qualitative results such as heat maps. He feels quantitative reports enable meaningful conversations, so he can clearly see what percentage of projects have been completed, what is pending, and how to align dates on specific timelines.
On a quarterly basis he meets with the executive management and discusses progress from a high-level, strategic roadmap perspective. He explains, “I came up with 11 initiatives we want to accomplish in 2019, so I give the executive management a state of where we are. I stick to a 12-month roadmap focused on how we help shape the organization by focusing on strategic and technical goals and starting with a baseline of maturity.”
GROWING A STRONG TEAM
Iqbal has grown his team from four to eight members and plans to leverage employees outside of his team to help ensure strong security through innovative programs. He comments, “We plan to build a program called Security Champions that will be across the entire organization, where we leverage one person from each business entity. We will follow the model of train the trainer, so security champions become the bridge between security and the business entity they represent. They will help to run initiatives on our behalf and will be a soft extension of our team.”
To retain talent, Iqbal relies on three things. First, he says there should be a clear definition of the responsibilities for each role. Instead of having people wear multiple hats, he makes sure they have a clear mission of their role and what they are responsible for. Second, he ensures each member of his team has a plan to grow their career. This could include sending them to appropriate trainings based on skills they would like to acquire. Third is making sure the compensation plan is aligned with the market and no gaps exists in terms of perks or salary.
He says, “My goal is to help my team know what their growth plan is. If someone is more interested in application security, then we need to make sure they are aligned to those initiatives and projects. I help them at a personal level by understanding these growth plans and their desired career path, making sure they are compensated in the right manner, avoiding micromanaging them, and giving them space to improve and grow. My philosophy is to empower them to mature and grow at their own pace in the direction they are interested in going.”
CISO TIP OF THE DAY
Iqbal believes in shifting corporate cultures to avoid over-reliance on computer-based training tools. Instead, he designs a comprehensive, interactive process and program. For example, he writes a ‘CISO Tip of the Day’ that is sent out to the organization. These tips may be related to something on the news or a relevant topic to employees’ everyday lives. He does not only focus on security from a corporate standpoint, but focuses on how security impacts their personal lives, whether it is protecting kids online or how to responsibly use social media. This opens communication channels between security and the rest of the organization and makes more people feel responsible for security.
TRANSFORMING BUSINESS LANDSCAPE
Threat vectors and motivators are constantly changing, and Iqbal believes a strong and embedded process and security culture help manage those risks, rather than relying on technologies. He explains, “I’ve seen some organizations look to technology tools to solve their problems and address risk. However, if you aren’t addressing culture at an organizational level or you don’t have processes that can be easily adopted or workflows that can be easily incorporated, then fancy tools will just collect dust on shelves. There is a clear gap in the market to keep up the pace with the industry and business. I look at transforming processes that are frictionless and user friendly, and that incorporate initiatives, so you are able to achieve value.”
Subscribe
Stay up to date with cyber security trends and more

