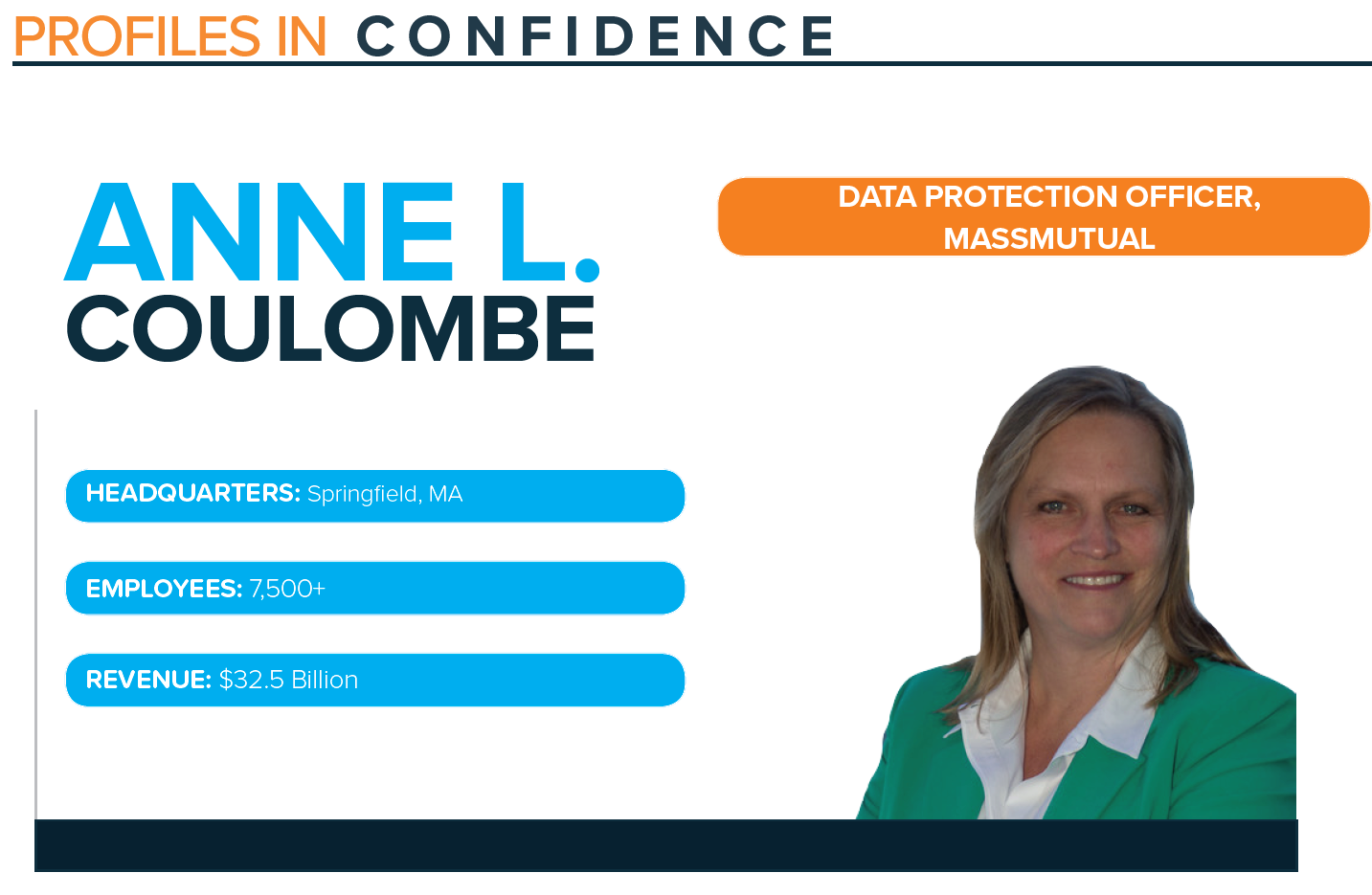
Profile: Anne L. Coulombe, Data Protection Officer, MassMutual
Published On: June 24, 2020
VIEW ANNE'S PROFILE
VIEW FEATS OF STRENGTH MAGAZINE
Information security has been woven into Anne L Coulombe’s extensive career for over twenty years. Coulombe currently works at MassMutual, where she started as a Business Information Security Officer (BISO) which then grew into her current role as Data Protection Officer (DPO). As BISO, Coulombe took elements of typical CISO responsibilities and applied them to a particular line of business. As DPO, her scope is broadened to the enterprise but narrowed in focus to protecting data.
She explains, “My responsibilities from BISO to DPO changed in part with the relationship between myself and the lines of business. From a BISO perspective, you are considering security elements, attack surface and controls linked directly to where the business is headed. As the DPO, I focus on protecting the data itself. Data is a broad definition from classification to inventory, to tagging and exfiltration tools for data loss prevention. In some ways I’ve narrowed my focus. On the other hand, there is opportunity for broad influence across the entire enterprise.”
FORGING A DATA PROTECTION ROLE
Coming into the DPO role, Coulombe had an opportunity to forge a new program spanning many departments and program areas. In her day-to-day, Coulombe focuses on securing customer and company data while minimizing the proliferation of restricted data throughout the environment, reducing business risk, decreasing the cyber-attack surface and securing core business processes. Working at a large company, Coulombe’s role is to unite data protection in cybersecurity and work with partners in compliance, privacy, law, enterprise risk and data governance. She also spends time educating employees and providing awareness regarding the data protection program and how every employee has a role in protecting data.
She comments, “A Data Protection Officer focuses on cybersecurity, yet crosses into privacy regulations and laws that exist in different geographies. Part of the role is understanding how all of those pieces and parts come together. It’s like a puzzle that you have to put together over a period of time. Not an easy role for somebody to walk into on day one. The best is to gather experience in different areas of business, cyber security and privacy and then bring it together to be the DPO.”
The role relies on being business-minded in order to service enterprise needs while reducing risk and must align the business desires with what data is most relevant and important to secure and protect. Being a strong communicator is vital, and influence management skills are used daily while working with other groups within the organization.
Coulombe continues, “The role could be for someone who came out of privacy and added cybersecurity or somebody out of cybersecurity who has added privacy or even worked directly with a set of regulations. In my case, I prepped for GDPR as it came into force with the European area of a previous employer. Someone coming into this role must be business-minded and a good communicator. In this role you are constantly evaluating what data type and quantity need to be secured and ensure consistency. It’s important to understand influence management because it is a role that includes extensive awareness and working with multiple groups.”
UNDERSTANDING THE ROLE OF DATA PROTECTION
Data protection functions have often been wrapped into a Chief Information Officer or Chief Data Officer. Coulombe explains, “Both of those roles in my opinion are slightly different. A Chief Data Protection Officer is somebody who has CISO-type skills yet is focused on data and protecting it in a variety of ways. Not just to focus on understanding what data and its classification, but now its use, how the data is replicated or transformed, the geographies in which the data lives, data flows between systems and access controls, and assessment of how it’s protected. Who and how access is granted and controlled is also a portion of the role.”
She continues, “My role is similar to being ‘glue’ as much of what I do is piece together both similar and conflicting data protection needs and ensure communication between different functions within the enterprise. Data is incredibly critical. If you wish to go back to the very basics, one for me is to make sure that there is a clear and well- communicated data classification. Everyone understands the classification, focus on the most critical data such as SSNs; everyone knows what they need to protect these SSNs at all times and in all uses.”
One key aspect of data protection programs is the strong alignment to corporate business goals in order to establish clearly defined deliverables and work towards improving and positively impacting the organization as a whole. Coulombe explains, “What I do ties directly into the company mission and vision, which includes securing customer data. It’s security, it’s protection, it’s enabling, it’s helping. It’s educating. As a mutual insurance company, we protect customers and company data in a similar manner, as it is foundational to the to the way that the company operates.”
LEADERSHIP
Constant learning and career evolution are Coulombe’s top priorities for her team. She says the methodology for achieving that differs person to person, depending on the individual and their learning style. For some people, being immersed at a conference for days provides them the appropriate training and growth, whereas others may need more technical hands-on trainings, or to spend time with an online course. Coulombe leverages a diverse set of mechanisms from an educational standpoint to accommodate how each individual on her team learns differently.
Providing leadership to her team is not a one-size-fits-all approach. Coulombe explains, “My leadership style varies. I say that because I’m a pattern watcher. I see trends and anomalies very quickly, and that’s a net advantage. It also means that from a leadership style, I must plant many seeds so people around me are able to come to some conclusions themselves and understand the path forward. Part of that is being able to open people’s eyes to what they may not have seen at first or second glance. There’s some tough love as well, by making sure that people around me, including my direct reports and other people I work with, stretch themselves. It’s being able to help them through those different endeavors. I activate interest and hidden skills in other people as there is no way to succeed in cybersecurity without a team working together.”
To ensure Coulombe herself continues to grow and learn she absorbs information from others, reads relevant publications, or listens to audiobooks. Along with focusing on key corporate goals to expand and innovate the data protection program, she is also focused on the CCISO certification, an industry-leading program that recognizes the real-world experience, something she is hoping to achieve by the end of 2021.
BACK TO THE BASICS
Coulombe says the definition of back to the basics does not mean go back to your tried and true software. Since threat actors are savvy and adaptable, we must adopt a new view to create edges where edges may not have been before or soften some things that may have been hard.
She comments, “There is some reality of having to secure the basics, absolutely. However the method in which you do so must include non-conventional controls. Threat actors already understand the basics, and they target a company for monetary gain or disruption purposes. They know what your typical large company is utilizing in terms of services and different software, therefore a layered approach reduces access to both easy and critical asset targets. Think like a threat actor targeting your infrastructure or your data, it helps us come up with methods to trick and catch the bad actors, be creative and be a step ahead as often as possible.”
Subscribe
Stay up to date with cyber security trends and more

