READ THE MAGAZINE
READ JOE'S PROFILE
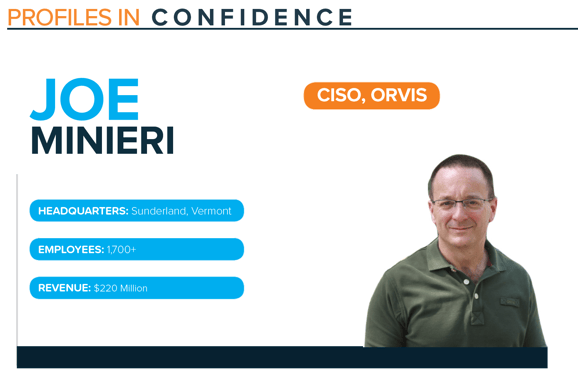
Joe Minieri’s first involvement with information security was while building and maintaining an internet e-commerce infrastructure in the mid-1990s, where he secured the network and monitored for suspicious behavior. From there, his career in information security blossomed as he progressed into leadership roles with growing responsibilities and strategic direction.
In 2006, Minieri became the Information Security Officer at General Dynamics, a global aerospace and defense company, where he had strong support to mature the information security program. The organization’s leadership believed in making investments to ensure they became a center of excellence for information security. Since only a limited security function existed, Minieri was tasked with coordinating security across the organization to push out standards, develop a robust program, and ensure the entire workforce recognized the importance of being secure.
After leaving General Dynamics, Minieri worked at L.L.Bean to help re-build their security program, address regulatory issues, invest in security program components from the ground up, hire a productive team, and establish a strong forward-looking plan for growth and innovation.
In 2019, Minieri became the CISO at Orvis, a Vermont-based fly fishing and outdoor product and services retailer. At Orvis, Minieri is responsible for the entire security strategy, the execution of security and regulatory compliance, incident response, as well as overseeing fraud prevention capabilities.
FOCUS ON BACK TO THE BASIC SECURITY
Minieri’s theme for the security program this year is ‘Back to the Basics’. He says, “First, I am ensuring that my security program covers the basic requirements sufficiently. There’s a number of good standards and guidelines available. I start by trying to demonstrate how I measure up to the chosen standards. Often, processes that were implemented years ago may become laxly implemented now. Sometimes we think we’re doing something completely, but not testing for thoroughness. When we test, we find out we’ve been missing things. This is how to identify gaps that need to be filled – either by reinvigorating a process that’s become slack or by finding a new piece of technology that does something we’re missing.”
In order to determine the organization’s security maturity, Minieri’s first step was assessing specific facets of the security program including processes and policies in place. He was able to identify where gaps existed and devise a strategic plan to take actionable steps towards increasing maturity.
He is also focusing on maximizing the investments in their environment. Similar to many CISOs, Minieri inherited technology and processes that were purchased and implemented by other people. He explains, “I’m inheriting the results of the implementation of someone else’s vision, or, worse, an implementation without a vision. Some of the investments may have been forgotten about by current employees or purchased by people who are no longer at the organization. In a new environment, you may need to sit down with finance to see what you’re paying for and taking a bottom-up approach to the budgeting process.”
To ensure he is maximizing their investments, Minieri first looks at everything from hardware to software and tries to whittle down the portfolio to only essential products. This may require a balancing act of removing several products in order to replace them by just one investment. By approaching it in this manner, Minieri is armed with strong justification for his decision.
INVESTING IN NEW TECHNOLOGY WHILE FOCUSING ON THE BASICS
Minieri recommends surveying all investments you already have before purchasing anything new. By doing so, you are able to see if there’s potential to leverage an existing investment by operationalizing certain functions instead of having to purchase a brand-new technology.
Minieri comments, “I have found that we often already have the products we need in place; they may not be completely deployed or efficiently operating. Here, I’d invest time to tune an existing platform. I may already have a solution that will get me most of the way toward meeting my objectives. If the survey reveals the products are obsolete and need to be replaced, then I can show savings by decommissioning old gear and unused software. In a tight budget cycle, I’ve often been able to get funding on new projects by showing an overall savings in my budget through sunsetting old technology.”
An important investment to evaluate is a Managed Security Service Provider to determine if the service they provide is still necessary and functioning appropriately. Minieri explains, “I’ve been able to in-source some functions at a lower cost while providing an equal or better service; this is a no-brainer. For services that we’re not ready to in-source, rebidding the service and finding a better provider at the same or less cost has also been very successful for us. Once your product portfolio has been optimized, you’re in a much better place to start thinking about what new technology you really require. By showing that you’ve maximized investments previously given to you, you’ll have an easier time justifying new acquisitions.”
SECURITY IS BUSINESS AS USUAL
Minieri likes to use the phrase ‘security is business as usual’, where the security program is streamlined and able to keep pace with the business transformation in a seamless manner. This occurs when processes and policies are in place and the team is efficiently operating to a point where it becomes muscle memory for them to execute.
Minieri says, “When I’ve been able to help mature a security organization to this level, we then have the bandwidth to work with the business to understand what they need and, usually, have it ready when they need it.”
LEADERSHIP STYLE
As a volunteer Firefighter/EMT, Minieri must making fast-thinking critical decisions, something he leverages in his work as a CISO.
He explains, “As a volunteer Firefighter/EMT I’m often part of a team making critical decisions that affect people and their property. We rarely have time to ‘meet to prepare for the meeting’ but instead, are quickly assessing a situation, sizing up our resources and tackling the problem right away. This translates to cyber incident response activities easily, but also more mundane work like prioritizing and executing tactical tasks.”