CISO Q&A: Cybersecurity Budgets
Published On: December 15, 2022

We asked budget questions to our community of Feats of Strength CISOs. These include CISOs who were previously featured in the magazine and have continued to contribute on a regular basis.
These experts share their thoughts on hot topic budget areas such as justification, focus areas, and more. The benefit of hearing directly from CISOs is learning from their past experiences when dealing with cybersecurity budgets and how they approach resource distribution and spend. As one of the more challenging areas that security leaders are responsible for, the more we hear from our network of CISO peers, the better informed our community will be. 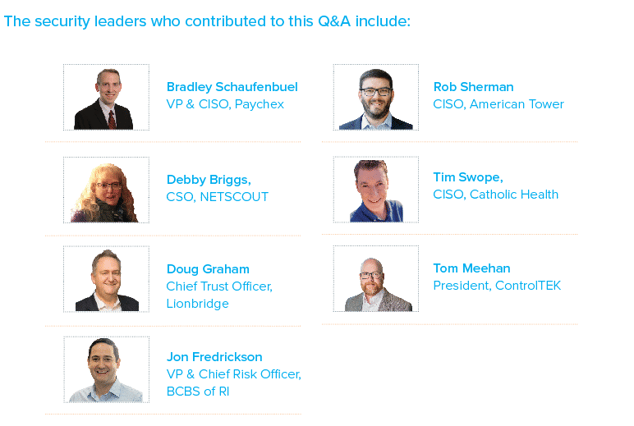 What are the best ways to justify cybersecurity spending to board and executives?
What are the best ways to justify cybersecurity spending to board and executives?
Bradley Schaufenbuel: I would suggest leveraging an economic risk quantification model such as the Factor Analysis of Information Risk (FAIR) to illustrate unmitigated cyber risk as well as the impact of spending proposals in mitigating those risks in terms of dollars and cents. Finance is the language of business, so I have found that presenting risk and risk mitigation efforts in economic terms resonates better with a senior leadership audience.
Debby Briggs: The best way is to engage with the board and executives in business terms. You need to explain what the risks are to the business, and what are the potential costs of not spending the money. It is always good to know your current IT Security spend as a percentage of IT spending, and as a percentage of revenue, against your peers.
Doug Graham: There needs to be an overarching plan that fits with the business plan and objectives, not just a series of tactical asks. In most cases, executives will ask the question, “what if I don’t do this thing” to the extent that you can answer that question you should. For companies that deliver B2B services, it’s important to channel the fact that there is an expectation from the customer that certain security measures are in place. When we tie security to revenue, or more appropriately draw the link between having adequate security and not losing revenue it can help to make the case.
Jon Fredrickson: It’s in the form of a non-technical business case. It needs to always show an ROI. Either directly (process improvement, user experience, etc.) or indirectly (mitigating a quantified risk).
Timothy Swope: World, national and business area (healthcare, retail, etc) threats and risks that directly affect your industry should drive the need for expenditures to remediate and mitigate those risks. Often, there is a ROI as spending on cyber can reduce cyber insurance cost, litigation for breaches and other negative outcomes of cyber breaches.
Tom Meehan: It’s important for organizations to be able to justify cybersecurity spending to board and executives. There are several different ways that this can be accomplished, depending on the particular organization’s situation. One way is to focus on the value of preventing losses due to cyber attacks. This can include costs associated with data breach notifications.
What program areas are the most challenging for CISOs to acquire budget for? Why?
Bradley Schaufenbuel: Program areas where it is difficult to estimate and measure the impact of cyber risk reduction efforts are the most challenging to justify. An example of that is an investment in training and developing cyber security professionals. It is difficult (but not impossible) to estimate or measure how much cyber risk is reduced because an employee is better trained.
Debby Briggs: Most challenging is headcount, I know that this is not a program. I think the reason for this is that it is an ongoing cost, that if no longer needed goes against NETSCOUT’s philosophy and culture of, “Lean but not Mean”.
Doug Graham: In my experience, the softer aspects of managing the security program are the harder things to justify spend on. Things like GRC tools or tools that don’t directly reduce risk (like technical tools might) tend to be a harder sell because the value statement is generally softer.
Jon Fredrickson: Emerging threats. Sometimes it can be difficult to convey why our existing tools are not “good enough” for the current situation/threats.
Timothy Swope: Staff - cybersecurity staff are in great demand and are costly. In addition, tools that give proactive cyber attack information are often hard to show the ROI. Finally, GRC (Governance Risk and Compliance) is difficult as it is not “in the forefront” of cyber news.
What advice would you give to a first time CISO who isn’t sure how to spread budget between people, technology, processes, etc.?
Bradley Schaufenbuel: I would suggest investing in people first, followed by processes, followed by technology. Technology is useless if you don’t have people to implement and operate it. A process is useless if you don’t have people to execute it or technology to facilitate it. As the Target data breach illustrated, you can have plenty of people and fantastic technology, but if you don’t have a well-defined process for people to respond to alerts generated by technology, attacks go undetected. And we have all seen shops filled with undeployed or misconfigured technology due to a lack of people and/or processes.
Debby Briggs: My advice is that you need to determine where your greatest risks are. If you don’t have people, who is going to provide the training programs, or use the technology? As a general statement, people would have the largest budget.
Doug Graham: I wouldn’t advise parsing a budget this way, I’d advocate that CISOs talk to capabilities and understand that there is a people, process and technology underlying most capabilities. We should sell the capability value and price in the necessary people process and technology components – otherwise we risk getting funding for things like tools and not funding for the people to run them.
Jon Fredrickson: Focus on people first, then processes, then technology. Buying tech is much more difficult than attracting and retaining top talent.
Rob Sherman: Make sure you really understand the company and where cybersecurity fits into the business model before deciding where to prioritize your spend. There is no “one size fits all” model to identify where to put your dollars. Second, that old IT adage of people-process-technology also comes into play. Security tools often seem like the best place to prioritize spend. But without the people and processes to implement and respond to alerts, the tools could become shelfware. On the flip side, especially in today’s hiring environment, it may not be possible to get the people you need, so that could push to a reliance on additional technology solutions.
Timothy Swope: People and training 45%, process 20% and technology 35%.
Tom Meehan: 55% to people, 20% to training, 25% to technology.
What area will CISOs see the biggest budget increase in 2023? Why?
Bradley Schaufenbuel: The areas of largest investment are unique to each organization, as the risks they face and the controls they have in place are different. That said, the areas my peers say they are investing in most in 2023 include zero trust architecture implementations and ransomware prevention and recovery improvements. The reasons for these areas of focus are obvious. Most attacks rely on compromised credentials, making zero trust architecture critical. And ransomware remains one of the most pervasive and disruptive attack types and is growing exponentially.
Debby Briggs: With the talent shortage, and increase in salaries and competition for employees, your people costs will be one of the largest increases. There are technologies like zero-trust and deep packet inspection that will improve our ability to reduce our attack surface and add greater visibility.
Doug Graham: This very much depends on the overall maturity of the program. Frameworks that are based on maturity will naturally drive people to a relative maturity of 3+ on a 5 point scale and where companies are operating below that I would recommend that they spend in this area. Regulatory and legal aspects including privacy will continue to drive spending – they are often the easiest to justify as well.
Jon Fredrickson: Hopefully investing in their people & workforce development. I still think we’re in a very competitive job market, so focusing on how to keep your team engaged, trained and sufficiently compensated should be top of mind.
Rob Sherman: 1) Regulatory & compliance given the pending SEC & DHS-CISA requirements 2) Supply chain/3rd party risk management as companies begin to look deeper into their supply chains and realize that there is work to be done to secure those paths into the network.
Timothy Swope: AI tools that give actionable information for operational decisions - these give a proactive cyber posture.
Tom Meehan: In 2023, the area of cybersecurity that will see the biggest budget increase is artificial intelligence (AI). AI-enabled security solutions are increasingly being used by organizations to identify and respond to threats more rapidly and accurately than ever before. As technology advances, so too does the sophistication of cyber threats, making it necessary for companies to invest in AI.
What is your approach to investing money in purchasing new technologies?
Bradley Schaufenbuel: We sort all cyber risks in our enterprise risk register by the amount of unmitigated risk. Where there is a cyber risk with an amount of unmitigated risk that exceeds the appetite established by the board of directors, we search for solutions that mitigate that risk. If that solution is the implementation of a new technology (note: many are not), then we follow a systemic process to set forth requirements for a technology solution, determine which vendors offer solutions that meet those requirements, and then evaluate each vendor’s solution via a proof of concept or proof of value. The solution that best meets our requirements at a reasonable cost is selected and implemented.
Debby Briggs: I ask, what are our greatest risks?
Who can we reduce these risks?
What does the threat landscape look like, and does this require me to look to new technologies?
What are the business goals. and how can security support and protect them?
Doug Graham: I like to work with early stage companies that have a direct fit for solving a tactical need. Typically by getting in early I can shape the results to fit and achieve good value for the my program as well as for the technology company – we call these design partnerships.
Jon Fredrickson: The purchasing of new technologies is always last on my list. This will always come after we assess our current toolsets and processes to ensure we can’t cover the gap more efficiently.
Timothy Swope: For healthcare - I define the best possible technologies that support patient privacy and safety.
Tom Meehan: When investing in new technology, it is important to look at the long-term benefits of the purchase. It is necessary to consider how this technology will help improve workflows and processes, as well as whether it has potential to increase profits or reduce costs.
Subscribe
Stay up to date with cyber security trends and more

