Assessing the maturity of your vulnerability management program
Some of the most notorious data breaches to hit the news in recent history can be attributed to organizations failing to address known vulnerabilities in their environments. Combined with the significant costs that can result from a data breach, how your organization is managing vulnerabilities needs to be a top priority.
When it comes to addressing your organization’s vulnerabilities, deploying a scanner, entering in IP ranges, and scanning periodically, is no longer sufficient within a threat landscape evolving every day. Shifts to cloud computing and remote work have created an even larger attack surface for an organization to take into consideration. Some key questions to ask are:
- Where is our critical data located?
- What are our critical systems?
- Who owns these systems?
- Do we know the vulnerabilities associated with these systems?
- When was the last time this system was scanned for vulnerabilities?
If you are struggling to answer any of these questions, it may be time to give your vulnerability management program a deeper look.
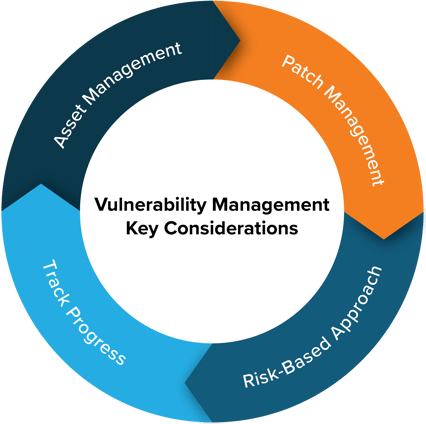
Key Considerations
Asset Management
Without having a clear picture of all organizational assets, being able to successfully monitor and address the vulnerabilities associated with these assets will become an impossible task. Asset management in the traditional sense may include building a new system, deploying an agent, and tracking in a centralized asset management system. However, such a simplistic definition of what constitutes an organizational asset is no longer sufficient. Does the organization have an application inventory to ensure that third party applications are receiving updates in a timely fashion? Do we have an inventory of cloud services that are in use? Are there other third-party vendors that we are sharing our data with? The level of understanding and clarity your organization has to these types of questions surrounding asset management are the benchmarks of a mature program.
Patch Management
Like asset management, patch management is a critical component of a successful vulnerability management program. When it comes to assets owned by the organization, vulnerability scanning should act as a system of checks and balances to make sure assets are being patched properly, identify potential gaps in coverage and assist in identifying areas where a patch may have failed to install. Where patch management becomes more difficult is for assets that may fall out of the organizations control or responsibility to update. For example, you are using a third-party Customer Relationship Management (CRM) application that is exposed to the internet and stores sensitive customer data. Does the contract in place with the vendor address how identified vulnerabilities will be addressed? Are communication channels in place between the vendor and organization to disclose vulnerabilities and remediation efforts? In a scenario such as this, your organization needs to have processes and controls in place to ensure vulnerabilities are addressed and patches are continuously applied. As organizations start to move business critical processes to the cloud and SaaS applications, how these cloud service providers are performing patch management on their systems becomes a key consideration.
Taking a Risk-Based Approach
One of the biggest concerns that we come across with customers when discussing vulnerability management is time and resources. It’s common to feel overwhelmed when looking through vulnerability scan results and seeing thousands of findings spread across what could be hundreds or thousands of assets. This is where taking a risk-based approach to vulnerability management can be a valuable tool to make sure calories are being burned in the right areas. There are various ways that a risk-based approach can be implemented and will be different for each organization and environment. Consider the following scenario:
A recent scan discovered that Server A and Server B are both vulnerable to the same zero-day vulnerability. Server A hosts a public facing web application containing sensitive information, while Server B is an internal server isolated on its own virtual network.
Now ask yourself, which poses a greater risk to our organization?
Measuring Success
Tracking the progress of your vulnerability management program is another key piece of the puzzle. We need to ensure that the program and the processes continue to mature as our environments and the threat landscape continue to evolve. Having the proper key performance indicators (KPI) in place and tracking over time is a great place to start. While tracking KPIs is a good jumping off point, it is also important to make sure that they are distributed to a wider audience (key stakeholders, executive teams). Trending metrics over time can be a great way for security teams to showcase successes, and can be equally helpful to raise any concerns or roadblocks to ensure issues are communicated and resolved.
Conclusion
When it comes to vulnerability management there is no one size fits all solution. Every organization is unique, and therefore the vulnerability strategy needs to be as well. As we have discussed, asking yourself the right questions and dedicating the time, effort and resources to proper planning will ensure that your organization is set for long-term success.
K logix helps customers address vulnerability challenges through our consulting and advisory services. If you have any questions, don't hesitate to reach out to our experts.