VIEW ANGELO'S PROFILE
VIEW THE MAGAZINE
MANAGING THE COMPLEXITY OF AN INHERITED SECURITY PROGRAM
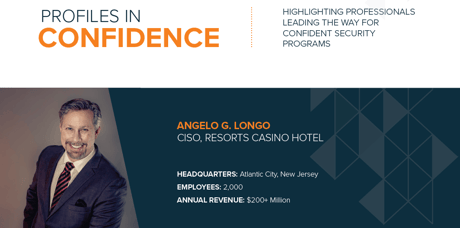
“A friend says that complexity is the enemy of security,” says Angelo Longo, CISO at Resorts Casino Hotel in Atlantic City, New Jersey. He continues, “I drive towards basic security in practice, so when we look at new buzzwords and marketing terms, we can understand if and how they will add value to our environment.”
Longo is new to the position of CISO at Resorts Casino Hotel. He inherited a security program built by a few predecessors. As one would expect of a program with more than one previous leader, there is some redundancy of products and potential for unnecessary complexities.
Longo strives to remain intent on streamlining the program to run more efficiently. As he explains, adding the latest and newest products to the environment does not always help. “Think about a motorcycle. You can have shiny rims and handlebars but you still need a good engine. The shiny stuff may add value, but in the end the whole motorcycle needs to be smooth and stable. The rider needs to be able to handle it.”
Whether Longo is analyzing new technology or existing investments, he prioritizes how those systems work and integrate with the current architecture. He also considers what they will enable in the future and constantly looks for value add. He comments, “Can these systems share data with each other? Do they integrate successfully, and do they support our five-year strategic plan?”
Longo points out the process of reducing noise may happen naturally and organically. He explains, “Look at the products that are implemented, but are not getting used. Examine the products used by only a subset of the team. For example, we had a product implemented to help with updates but only a few people on our team used it. The old method worked better and faster. Perhaps with education or training we could have more people using the newer solution. We also have to consider that a better idea for us may be to reduce expenditures and move that product out of our environment.”
TAKING FIRST STEPS IN EVALUATING A SECURITY PROGRAM
Longo came into an established security program with systems and procedures already in place, and had the opportunity to conduct extensive evaluations when coming on board. To help with these evaluations, he relied on existing team members to gain a clear picture of the environment.
He explains, “I needed to understand what the business is and how it functions. What are the tools we have? How do they work and where do they fail? These are the questions I needed to ask as I moved the company to a more strategic model. My understanding of how the organization worked was filtered through the people I had interactions with. My team is excellent, and they have been helpful in this exercise.”
Longo is focused on ensuring the organization’s security stack is built in a way that adds visibility and value to his program. He says, “I’m the consumer of the data these security products bring to the forefront. The operations team will operate them, but I am the consumer and I need to be able to make sense of the data as a whole.”
He continues, “It is a multi-vendor product stack in the environment. I am not saying I want to move to a single vendor, but I do need the data from all the systems to be presented in a way I can consume. I need to be able to understand that if three systems are alerting me about a threat, that it may actually be a single threat.”
THE GAMING INDUSTRY PRESENTS UNIQUE CHALLENGES
Traditionally, CISOs grow up in a specific industry, however Longo’s eighteen-year information security career spanned many industries, from defense contracting to finance, and manufacturing. This broad experience prepared him for the different challenges presented by working in the gaming industry.
Due to heavy regulation in the gaming industry, Longo and his team report into the audit committee. Longo explains how this makes sense for the company, and fits into his overall beliefs about how security should be structured in any organization. He explains, “I do not believe information security belongs under an IT organization. You must be able to look at security policies and procedures and everything within the company, not just from the standpoint of the wires. You have to understand how the business is structured in order to secure it. If you are in the IT organization, security becomes very tech-centric and compliance becomes focused on technology, security becomes focused on up-time.”
He continues, “The gaming regulations require that my position dictates framework and compliance to the CIO. That is really why I took on this role.”
Longo explains how the two groups - security and operations - co-exist in this arrangement. “I set the security standards. The operations team needs to adhere to the policies and procedures. Then I audit them for compliance. I do vulnerability analysis and penetration testing. We look at various aspects of the organization to determine abnormal user interaction.”
Longo recognizes the high-profile target placed on the gaming industry, both on and off-line, for attackers who see it as a cash-rich enterprise. He believes digital transformation, and the gaming industry’s increasing online emphasis, will present additional security threats and challenges.
“I believe the gaming floors themselves will become more mobile than they are now. Our clients will change and people who are gambling will have different expectations. We will evolve from a geo-centric point of view to a more mobile point of view. We are going to need to provide access to mobile users to make wagers, make deposits, and accept payouts. That will be an ongoing point of vulnerability for all of us in the industry. People will target our online services in different ways.”
Longo believes IoT presents its own growth opportunities for the gaming industry, and will bring unique security challenges to Resorts Casino Hotel. For example, he says, “At some point in time will you be able to ask Alexa to put $500 on the Eagles vs the Redskins? Probably, yes. Given that fact, what do we need to do to enable secure, safe, and legal transactions?”
These are the types of challenges Longo would like to discuss with peers. He says his goal for the coming year is to create a community of local security leaders in the gaming industry. He says, “As we drive towards industry compliance, I want to also establish a committee or group of security professionals that works toward making information security bigger and stronger at a local level.”